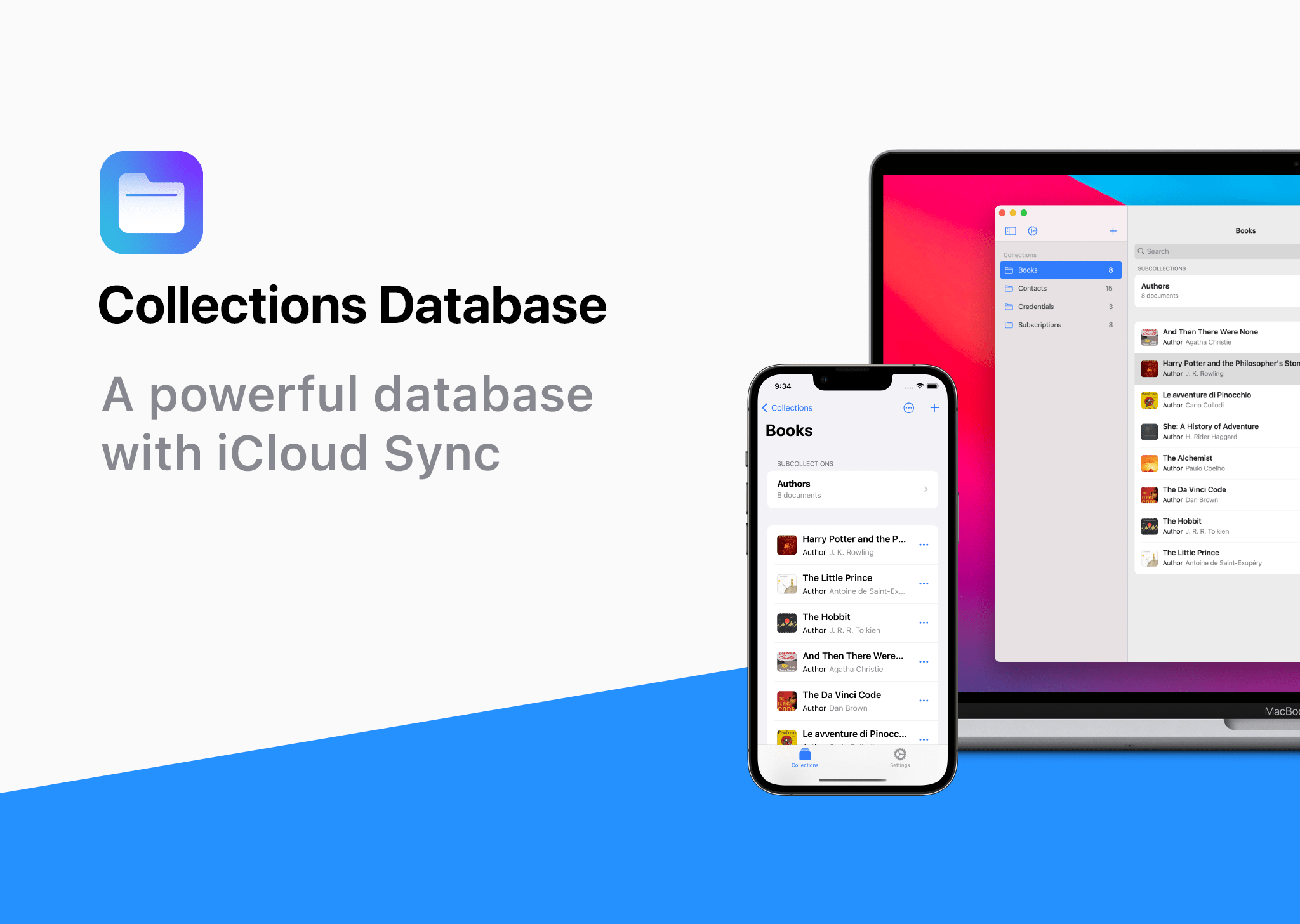
Collections Database is the premier personal database app for organizing anything and everything on your iPhone, iPad, and Mac.
The app features more than 20 field types, linkable sub-databases, reusable lists, and a robust customization system. It’s a powerful and flexible solution that makes Collections easy to get started with for beginners, while meeting the needs of advanced users too.
Collections provides essential templates to get started, including Expenses, Contacts, Subscriptions, Books and more. However, you’re always free to start from scratch by building your own custom templates.
A long, complete list of field types is available for your databases too. The set includes everything you’d expect from a modern database app, including Text, Number, Date, Picture - even Barcode fields. Collections can import spreadsheets from other apps, using its powerful CSV import functionality. Collections also offers quick filters, sorting, password protection, smart text-based search, and more.
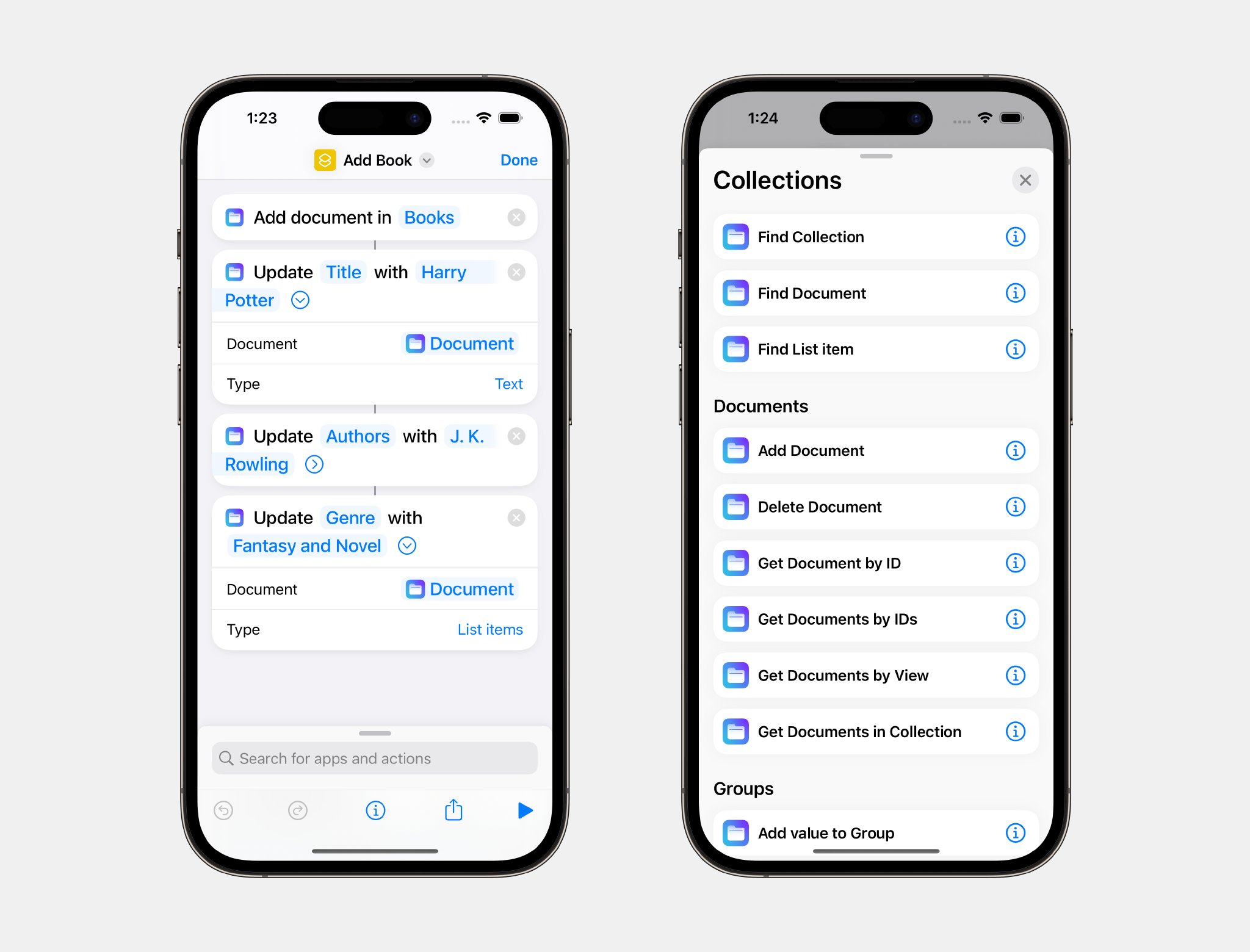
A standout feature is the extensive support for Shortcuts, which expands the app capabilities even more.
Collections is free to try, but by upgrading to the Pro version via In-App Purchase, you’ll gain access to an unlimited number of database entries and files, plus advanced filters. The Pro version also includes a unique visual formula editor the makes building complex formulas intuitive and easy.
The app is a universal purchase, so your purchase will be available on the iPhone, iPad, and Mac. At the same time, though, Collections has been carefully optimized to each Apple platform for the best experience on every platform.
Collections is regularly updated to take advantage of the latest Apple technologies and is privacy-minded. Your data isn’t collected or sent anywhere else.
To learn more, and download Collections Database visit the App Store today.
Our thanks to Collections Database for sponsoring MacStories this week.