Mountain Lion’s Gatekeeper
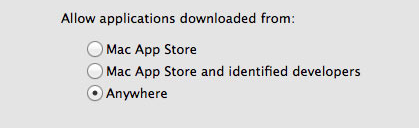
When the Mac App Store launched just over a year ago, many feared that it was the beginning of the end for running apps that weren’t approved by Apple on OS X. Jump forward a year and a bit and Apple has announced Mountain Lion, the next version of OS X that is set to launch this summer. One big feature of Mountain Lion is what Apple is calling Gatekeeper. It’s a new setting, aimed at both security and peace of mind. Essentially Gatekeeper will be giving users three options for controlling what apps run:
- Only allow applications from the Mac App Store to run
- Allow Mac App Store apps and those from identified developers
- Allow any app to run
By default, the second option is chosen, allowing apps from the Mac App Store to run, as well as those from identified developers. What’s an identified developer? It’s someone that has registered as a developer with Apple and receives a personalised certificate. They can use that certificate to sign their apps, so that Gatekeeper will allow the app to run. It also means that if the app is found to be malicious, Apple can order Gatekeeper to remove that app from any Mountain Lion machine. Mac developers Panic have written a long blog post explaining the feature in great depth, explaining how it works, why it’s needed and why Apple chose to implement it in this way.
The simplest thing Apple could have done would have been to make the Mac App Store the sole source for Mac apps, in the same way the App Store is the sole source for iOS apps, shutting off every other app distribution venue in the process. While this would have immediately solved the problem, you would have seen developers’ heads bursting into flame and flying across the room in rage. Why?
Although security is a vital feature for Apple, developers, and users alike, being unable to run unsigned code cuts a lot of really great things off at the knees. You wouldn’t, for example, be able to just download and run an open source project unless it had been submitted to and reviewed by the App Store. Highly disruptive software (think Napster or BitTorrent) may have not been able to exist on the Mac platform since it would have been likely to run afoul of Apple’s App Store guidelines. Major vendors such as Adobe and Microsoft might have withdrawn their support for the platform, being unwilling to cede 30% of their revenue to App Store distribution.
It isn’t all good news though, Panic is concerned that Apple may be implementing an “artificial gulf” between App Store apps and non-App Store Apps by restricting some new features to only those distributed on the Mac App Store.
There remains one thing that is of concern to me. Despite these great strides forward, Apple is walking a dangerous line with regard to features that are only available to App Store distributed apps. The two most prominent examples are iCloud and Notification Center. Cabel asked Apple if, thanks to Gatekeeper and Developer ID, App Store-only features would be eventually be available to signed apps that were not distributed through the App Store. There was some shuffling of feet and a “we have nothing to announce at this time”. It didn’t sound particularly optimistic.
Gatekeeper will no doubt be a hot topic of discussion in the coming months and we’re likely to see all sides of the debate argue about what Gatekeeper represents. ZDNet, for example, has labelled the feature as a “tool that restricts what the user runs, rather than a security tool that sorts the wheat from the toxic chaff”. Macworld also has an in-depth hands on article with Gatekeeper that is well worth the informative read.