It’s been ready for a while, but today, AltStore is finally available for iOS users in the EU.
Riley Testus, one of AltStore’s founders, had this to say about the launch:
This is a day I’ve been looking forward to for over 10 years.
I’m thrilled to announce a brand new version of AltStore — AltStore PAL — is launching TODAY as an Apple-approved alternative app marketplace in the EU. AltStore PAL is an open-source app store made specifically for independent developers, designed to address the problems I and so many others have had with the App Store over the years. Basically, if you’ve ever experienced issues with App Review, this is for you!
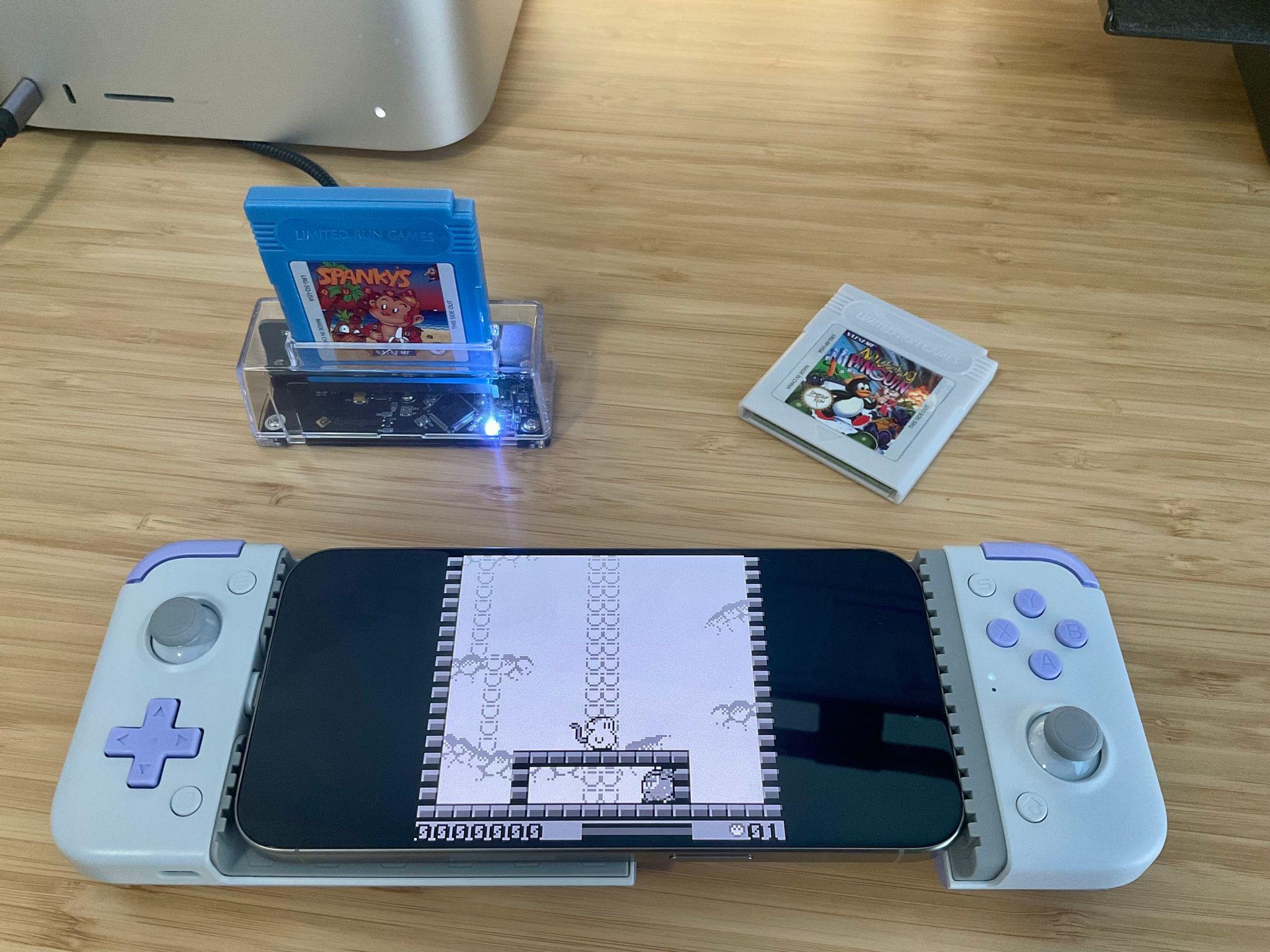
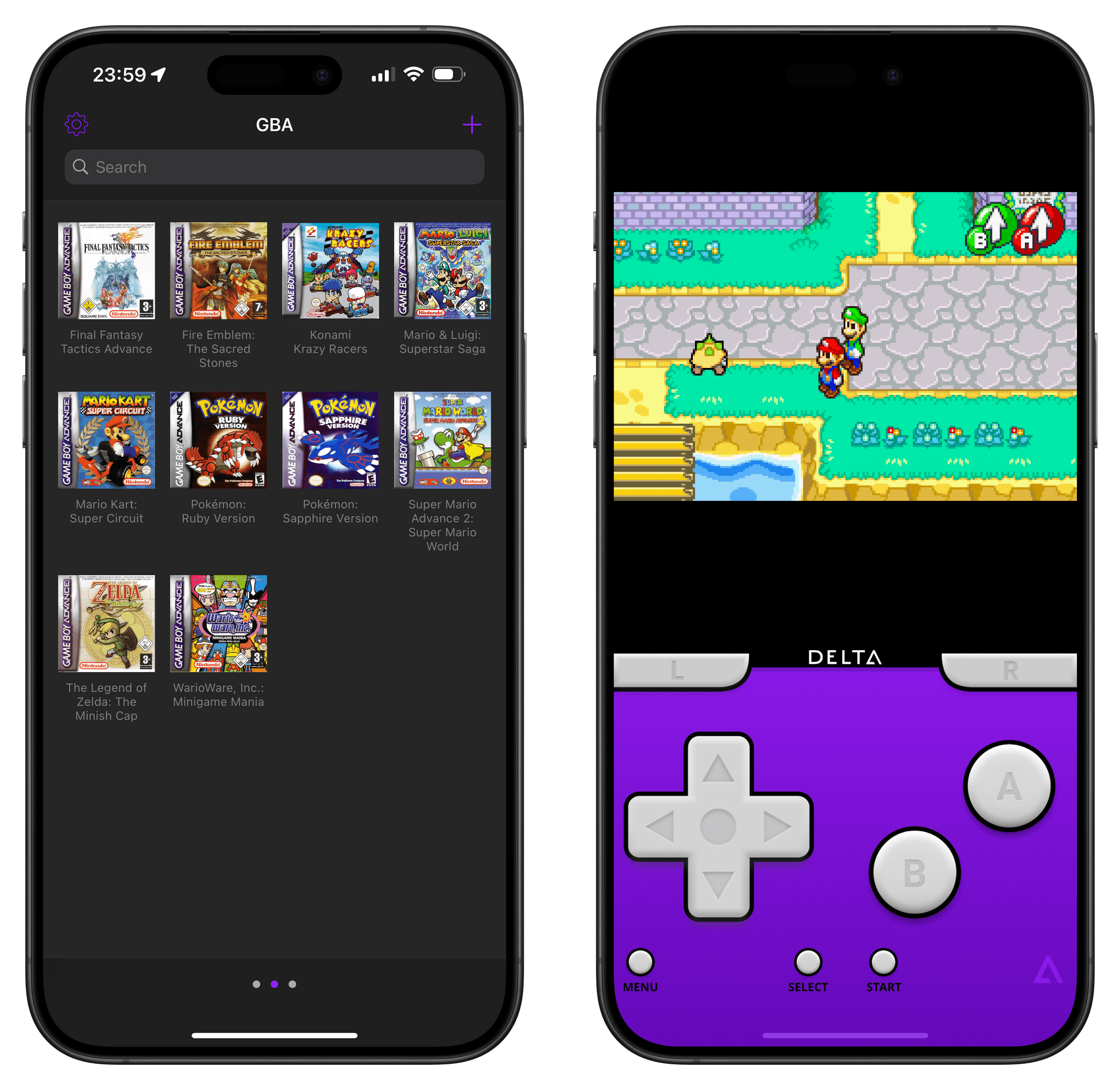
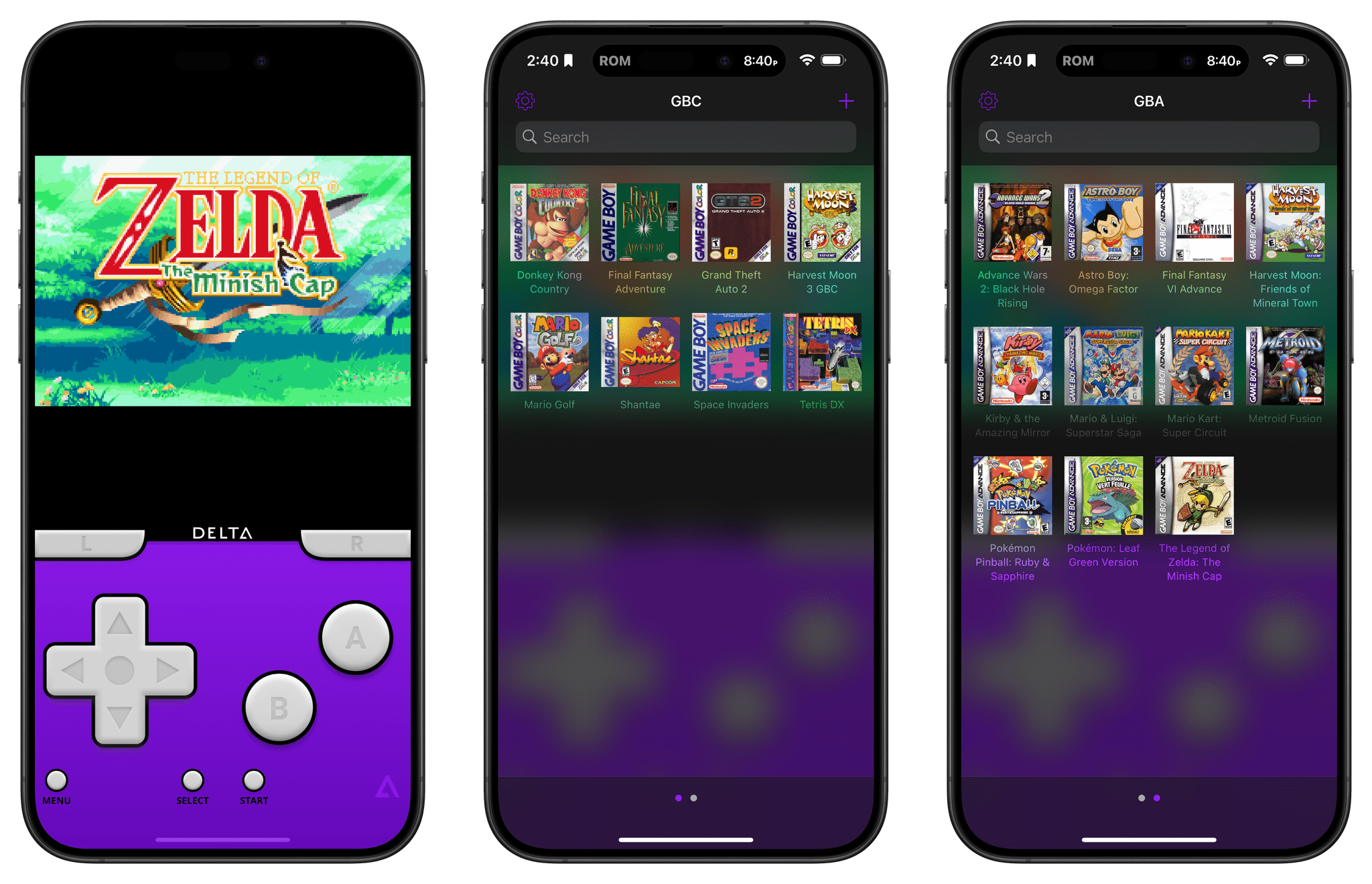
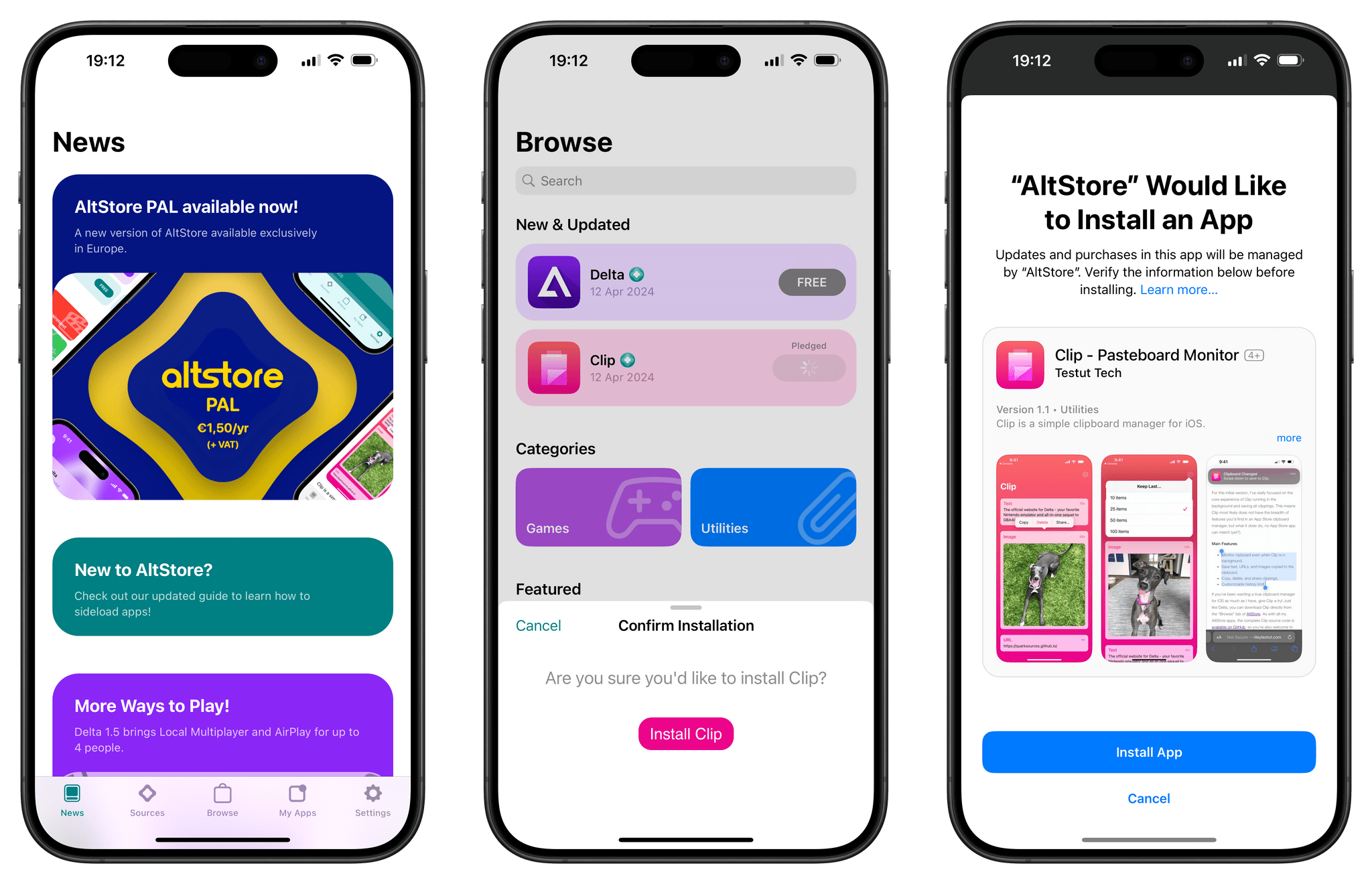
We’re launching with 2 apps initially: my all-in-one Nintendo emulator Delta — a.k.a. the reason I built AltStore in the first place — and my clipboard manager Clip, a real clipboard manager that can actually run in the background. Delta will be FREE (with no ads!), whereas Clip will require a small donation of €1 or more. Once we’re sure everything is running smoothly we’ll then open the doors to third-party apps — so if you’d like to distribute your app with AltStore, please get in touch.
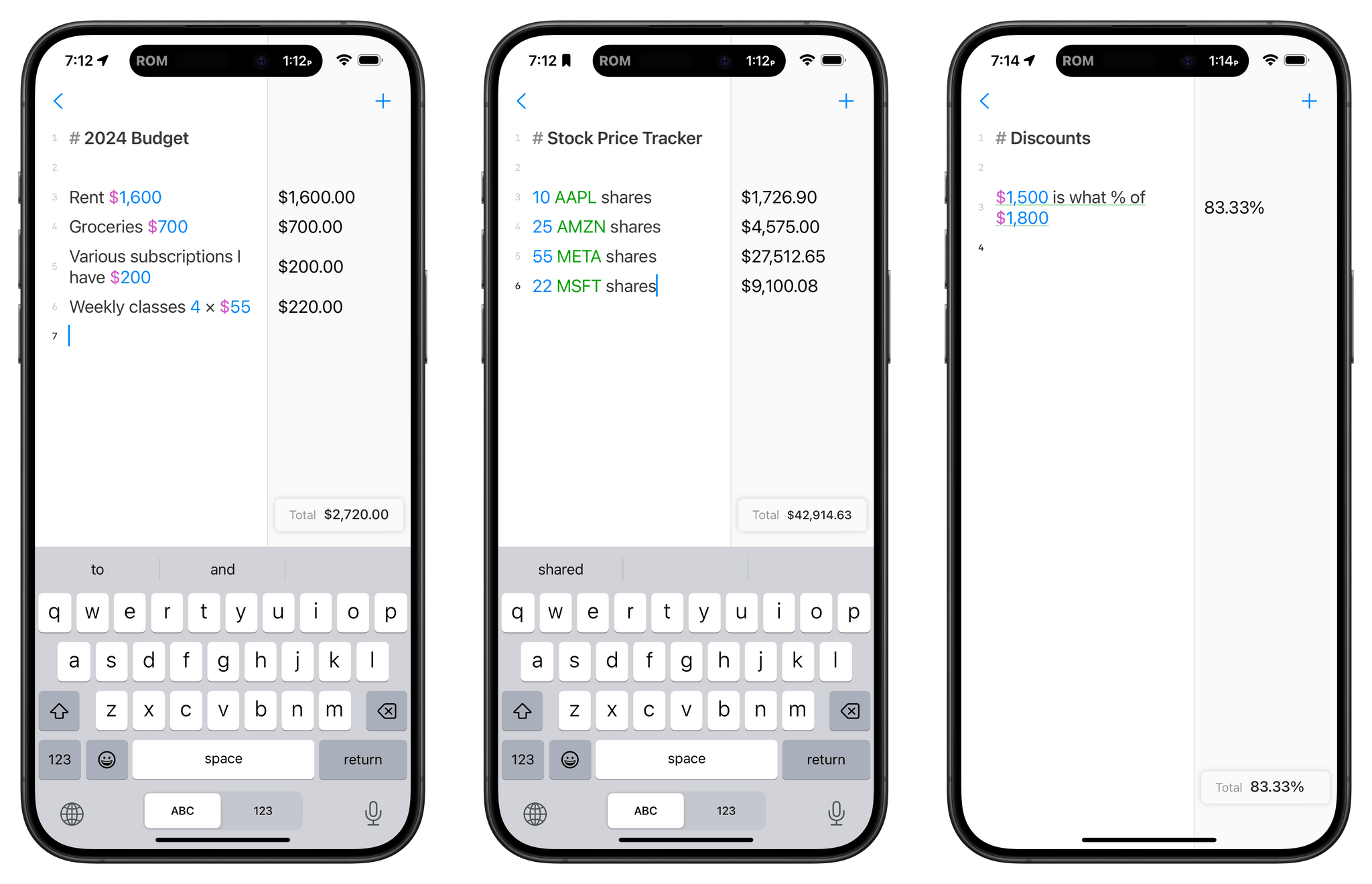
AltStore is a self-hosted solution, meaning once it starts accepting third-party apps, those developers will have to host and promote their apps themselves. From a user’s standpoint, that means:
…there is no central directory of apps; the only apps you’ll see in AltStore are from sources you’ve explicitly added yourself.
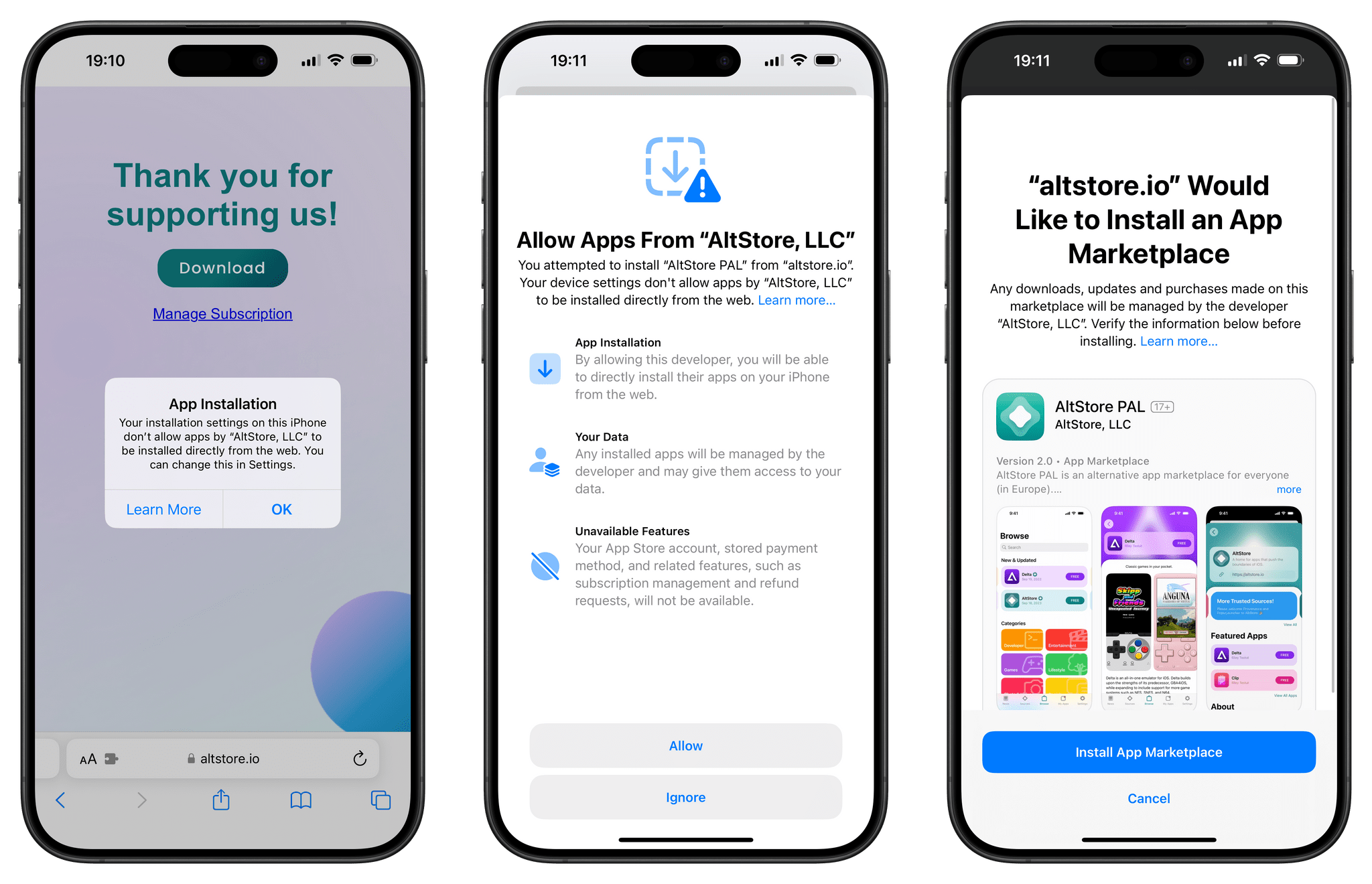
Also, if you’re in the EU and have US and EU Apple IDs, sign into the EU one and download AltStore. Then, you’ll be able to log back in with your US Apple ID if you want, and AltStore will still work.
As Riley explains, this is a lot like Apple’s recently announced web distribution feature in the EU.
The AltStore team envisions their marketplace as a place for apps from indie developers and those that Apple won’t allow on the App Store, like the team’s Clip app. AltStore will use Patreon donations as its payment system for paid apps, just like AltStore and Delta have been doing for years. Also, AltStore will not take a commission on Patreon donations. However, AltStore will cost €1.50/year to cover Apple’s Core Technology Fee.
It’s exciting to see AltStore live in the EU. I wish it were available in the US too, and I recommend reading Riley’s blog post about what motivated him build AltStore. It’s about more than videogame emulators, which I love. That’s maybe where AltStore started, but it’s about the iOS indie developer community, which I love even more.









](https://cdn.macstories.net/banneras-1629219199428.png)